20世纪初,卢芹斋(C .T. Loo,1880-1957)白手起家,逐渐成为第一个让世界文物市场里“中国风”劲吹的操盘手,此前,法国古董商的贡古尔兄弟主推日本艺术品,中国艺术在国际上地位不高。随着卢芹斋的买卖日渐红火,大量中国文物流散海外,卢芹斋也在国内招致大量批评声音。随着谭敬作伪集团冲击,以及不久后新中国的建立,文物走私途径中断,卢芹斋不得不清理藏货,结束生意。如今有关他的残存印象,仅留巴黎一座红楼和欧美博物馆藏品上标明的“C.T.Loo”标签,提醒着人们这些古董的共同来历,伴随而来的则是今人对卢芹斋毁誉参半的评价以及经他手流散海外国宝的归属问题。
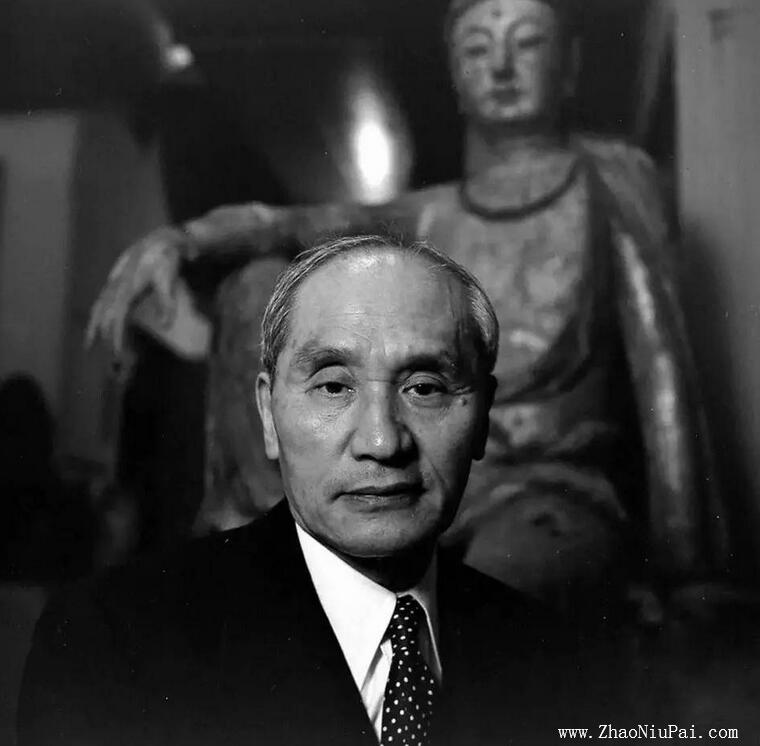
卢芹斋
卢芹斋简介
卢芹斋1880年出生于浙江湖州卢家渡,初名“焕文”,后改名“芹斋”。卢幼年失怙,初寄养于远房的堂叔家,后入南浔张家做仆人。张家大少爷,就是日后国民党四大元老之一的张静江。1902年,张静江任清廷驻法国商务参赞,张静江将卢芹斋携往巴黎。次年张静江在巴黎开设“通运”公司(Ton-Ying&Company),售卖中国的瓷器、字画等,将收入悉数资助了孙文,支援辛亥革命。
卢芹斋从古董店学徒开始,刻苦学习古董店的各项业务,又学说了一口流利的英语、法语,很快就受到老板赏识,卢芹斋逐渐出任掌铺了。辛亥革命后张静江回国协助孙中山,通运公司结束,卢芹斋开办了自己的古董店,成立了卢吴古玩公司。
恰巧这时又赶上国内清政府垮台,北洋政府执政,人心不稳定,故宫内的古物珍宝纷纷流失海外,卢凭着鉴别中国文物的本领,成功低价收购不少古稀珍品,推销到欧洲市场,一本万利。渐渐地,卢芹斋成为享有盛誉的中国古董鉴赏家,也成为欧洲华人中的名人。
此后的数十年,他以自己深厚的中华文物鉴赏知识和商业才能,启蒙性地把欧美收藏家们的眼光从中国装饰性瓷器引向了文化积淀深厚的中国墓葬艺术和佛教艺术。
随着其生意日隆的同时,是大量国内重要的文物走私流散海外,他在国内招致大量批评声音;且在文物买卖事业的鼎盛时期,却栽在谭敬的作伪集团手中,大大损失其名誉与信任度。而随着新中国的建立,文物走私和国际贸易中断,更使其国内文物来源断供,50年代初他不得不全部清货,结束生意。
1926年开始,卢芹斋在巴黎建造了著名的“巴黎红楼”,用文物营造的中国文化气氛极为浓厚,“红楼”的一、二、五层和地下一层的一部分已被巴黎市政府列为文化遗产。卢芹斋曾捐款资助过辛亥革命,在一段时间内,每天在红楼免费资助中国留学生一顿午餐。晚年的卢芹斋总结自己的一生充满了矛盾,他承认自己使不少国宝流失海外,又为这些国宝避免了战乱得到了保护而感到幸运。
1957年,卢芹斋死于瑞士,终年78岁,葬在妻子的家族墓地古何贝瓦。
卢氏古董帝国的崛起
20世纪初至第二次世界大战期间是国际收藏、研究中国艺术品的第一次高峰。清代宫廷藏品大量流散,考古出土文物不断涌现,国内古董市场迎来了一个空前繁荣的交易活跃时期,英、美、日诸国的收藏家、学者、文物商贩聚集北京城,抢购来自中国的珍宝。其中英国达维德、日本山中商会、法国卢芹斋、美国福开森皆为其中佼佼者。卢芹斋及其卢吴公司凌驾众人之上,号称中国文物市场的“古董教父”。
当时,西方人对中国的认识尚十分粗浅,其印象被当时风靡欧洲的“日本风”文物艺术品所掩盖。卢芹斋凭借多年的鉴定经验,认识到中国古代艺术品的价值。在针对欧美客户的来远公司开办之初,卢芹斋为迎合欧洲藏家的癖好,主营青铜器、石雕、瓦器等。此时,卢芹斋暗通国内代理商,在北京和上海建立公司分号,以便利向国外发货。1918年,卢芹斋开始经营美国分公司,其所经营的古董主要是石器、陶器和佛教造像等。历经40余年的时间,卢芹斋建立起一个倚靠民国政要为流通渠道,跨越欧美的世界性古董帝国。
卢芹斋的卢吴公司所以能够成功的一个要因在于卢和蒋介石口中的“革命导师”张静江关系密切。国民政府对于卢吴公司向海外贩运珍贵文物也就特别礼遇优待,常常睁只眼闭只眼。据有关部门调查,卢吴公司从国内运走的文物多达8000余件,而且均是珍品,有的品种国内已经无存。此外,卢芹斋还擅于处理与国内外重要藏家和机构的关系。据研究确认,海派代表藏家之一的庞元济部分藏品经由卢芹斋流往海外。一部分流散到国内私人收藏家手中,一部分则流散到国外各公私收藏机构,其中以流入美国各大博物馆为多,如弗利尔美术馆、底特律美术馆、纳尔逊-艾金斯美术馆、克里夫兰美术馆等。
卢芹斋的生意制胜关键不仅包括国内广泛的人脉、灵通的国际行情消息与精明头脑,还有积极举办、参与展览。如1934年和1935年,卢分别在巴黎和伦敦举办中国青铜和古玩展览以推广销路。他还趁1935年至1936年伦敦中国艺术国际展览会(为当时最大规模的中国文物海外展览)之时,将自己公司的藏品纳入其中。此外,卢芹斋还通过出版画册来笼络客户。
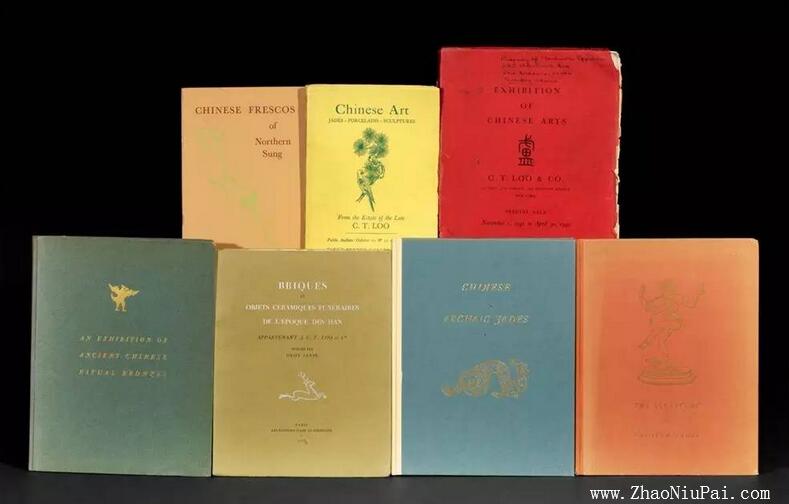
卢芹斋的藏品图录
这些早期的古董图录,其藏品品类之全,质量之高,绝不逊色于国内一流博物馆的规模。2012年,纽约佳士得拍卖行举行了名为“知识的追求:亚洲艺术品参考书(包括卢芹斋收藏艺术文献)”的专拍会,这些文献记录了当时尚存于世的墓室和庙宇,其中一些是因为卢芹斋生意失败而遭受破坏,甚至洗劫一空的。现在,这些画册成了拍卖场上的抢手货。其中卢芹斋1940年在美国举办“中国石雕展”时出版的展览图录,刊印了云冈石窟、龙门石窟、巩县石窟、天龙山和响堂山五大石窟的历代佛像精品(书中刊印的一些作品至今下落不明),该套图录估价仅为500~800美元,最终以5.62万美元成交。
旧时珍藏,而今流散
如果要追踪一百多年前的国宝流失及聚散状况,最直观的材料是古董商的家族档案、公司信件账目等。关于卢芹斋的研究,海外掌握其档案资料较系统。卢氏早期的业务档案,一部分藏于巴黎红楼,一部分藏于北京图书馆。后者系当年没收北京古董商的档案资料。另有在上海博物馆的材料,系没收卢氏的主要合作伙伴的档案。收藏在巴黎红楼的档案经罗拉女士编撰,后在香港出版《卢芹斋传》一书,阐述了卢芹斋作为国际知名文物商的坎坷一生。
虽然卢芹斋尽力掩盖他直接参与文物走私的事实,但这些明确史料仍能清晰重现这位神秘商人的生涯。杨仁恺先生在《国宝沉浮录——故宫散佚书画见闻考略》列举数件与卢芹斋有关的国宝:如宋人摹本《八公像图》、宋李公麟的《华严变相图》和《列仙图》、南宋米友仁的《云山图》、元初钱舜举的《王羲之观鹅图》、元赵雍临李公麟《五马图》等。而来远公司、卢吴公司的拍卖账单是最直接的原始记录,一般在账单上都标明日期、编号、件数、品名、买入价、卖出价。比如在一份长达77页的账目上,首页即列出“钱选花鸟”等28种拍品,全册所收古物的总成交价达235312.30法郎。另外,1913年1月21日伦敦拍卖账目记录了这桩以古瓷器为主的买卖,末尾特地以中文写明“毛利”10339.40法郎。只是这些账目中的名称一项写得十分粗率,如“钱选花鸟”一种,因钱选所作花鸟画不少,很难确定是哪一幅,所以对流散在外的文物书画作查证尚有不少困难。但对于某些知名度很高的文物而言,则证据确凿。如现存美国宾夕法尼亚大学博物馆的唐昭陵六骏之“飒露紫”“拳毛騧”,有资料表明系卢芹斋“购办”的结果(照牛排注:大约在1916年至1917年被偷运至美国,1920 年底此“昭陵二骏”被卢芹斋以12.5万美元卖给宾夕法尼亚大学博物馆)。通过这些泛黄了的旧资料,可以弄清一部分流散文物的来龙去脉,然而对此,每位真正的中国人都有着切肤之痛。
一位古董商人的“野望”
在卢芹斋之前,世界艺术市场中的东亚艺术还是以日本作品为主要代表,法国19世纪中后期的远东艺术古董商家几乎皆同时代理中国与日本的文物,之间并未有明确的区别。对于一个白手起家的文物商来说,他要在西方艺术市场中立足,只有树立起公司的品牌,开拓艺术品的种类,掌握国内文物的货源;最重要的是提炼并让世界认识到“中国货”的价值。终其一生,卢芹斋的确实现了这个目标。从国外主顾的角度看,卢确实是一位极好的供应商,使其免去了很多出入关的麻烦,是个名副其实的文物买办。但为人所痛恨的是国宝的大量流失与破坏,其中最为严重的是昭陵六骏、天龙山石窟佛雕。招致身后的骂名。
对于卢芹斋一生的评价,可借用大收藏家张伯驹先生一句话:“综清末民初鉴藏家,其时其境,与项子京、高士奇、安仪周、梁清标不同。彼则楚弓楚得,此则更有外邦之剽夺。亦有因而流出者,亦有得以保存者,则此时之书画鉴世故家,功罪各半矣。”卢芹斋将西方原来单一的中国瓷器艺术品收藏拓展到佛教雕像、石刻、青铜器、玉器、书画等多种门类。而在第一次世界大战期间,卢芹斋在无意中为中国雕刻开拓出崭新的市场,却也让石窟佛像陷入一场浩劫,众多集中国历代佛教造像艺术精萃于其中的石窟惨遭毁灭性破坏。如山西太原晋祠后山上的无头石窟,佛像处处身首异处,惨不忍睹,文物沧桑,莫过于此。
从罗拉所著《卢芹斋传》中透露的自述材料看,晚年的卢芹斋常常怀着矛盾的心情。他承认自己的生意致使不少国宝流失海外、遭到破坏,又为这些国宝远离更加恐怖的战乱而感欣慰。他认为,许多国宝名品终熬不过民国前后40年的盗凿贩售。
卢芹斋曾为自己辩护,认为自己不是历史罪人,因为艺术没有国界,与其勉强把很多宝贝留在中国,沦为有价的商品筹码,再遭盗劫破坏,不如妥善保管于国外的博物馆,充当“文化使者”,让更多人认知欣赏中国古代艺术的精美。这种充满矛盾的辩解当然不能让他脱身于批评的浪潮,当年与他有买卖关系的知名博物馆也被这种不光彩的跨国贸易笼上一层阴影。可是,世界级的博物馆收藏系统的建立过程中,又有谁能独善其身?卢芹斋曾于晚年向上海的文物管理部门捐赠藏品,但对他而言,无论从身份还是个人感情,回归故土都是无望的。
来源:中国美术报 作者:许万里 2016-11-12
如需注册Payoneer派安盈,欢迎使用【野猪尖的推荐链接】进行注册,成为我的推荐客户,后续在使用派安盈时遇到问题能获得专属咨询服务,也可协助申请1%或更低的费用优惠。请注意,若打开Payoneer官网来注册,是没有上述优惠的。Payoneer注册咨询,+微信号:ZhaoNiuPai
【野猪尖的推荐链接】 http://ZhaoNiuPai.com/Payoneer.html
复制上述链接到浏览器打开,或扫码注册Payoneer派安盈
【Payoneer派安盈申请教程:个人账户、企业账户、随心付虚拟卡】
======【Payoneer派安盈注册与使用指南,野猪尖整理于2013→2026年】======
【注册】→Payoneer个人账户注册教程 | 公司账户申请教程 | 地址证明和证件 | 注册被拒绝
派安盈个人和公司帐户的区别 | 如何注销P卡 | 买卖P卡的风险 | 更换密码及手机号 | 更换邮箱
【币种】→美元电汇 | 欧元 | 英镑 | 日元 | 加元 | 澳元 | 墨西哥 | 港币和迪拉姆 | 币种转换
【官方】→秉承公正、公开、透明服务 | 封号原因 | 最新政策 | 答疑手册(FAQ) | 手机App
联系客服 | 费用表 | 年费 | 如何减少Payoneer手续费 | 跨境收款服务商拷问
跨境电商论坛:2019年 | 2018年 | 2017年 | 2016年 | 2015年 | 直播回放 | 橄榄枝计划
【收款】→亚马逊绑定派安盈 | 更换收款帐户 | 收款方式对比 | 账户对账单 | 子账户和KYC证明
提前放款服务 | 跨境电商/外贸收款方式对比 | VAT缴费(答疑) | 如何评价Payoneer派安盈
最新平台:Chewy | Chewy入驻 | Trendyol及其它独家平台 | TikTok直播 | TikTok Shop
老平台:PayPal | Wish | 虾皮Shopee | 俄罗斯Joom | 东南亚Lazada | 非洲Jumia
eBay | 拉美Linio | 美客多Mercado Libre | 新蛋Newegg | 沃尔玛Walmart | 苹果开发者
法国乐天 | 法国CDiscount | 德国乐天、Real.de、eMAG、Wayfair、京东印尼 | 波兰Allegro
如何向Payoneer充值 | 如何用Payoneer派安盈收款 | 请求付款(答疑) | 收款审核时“待定”
Payoneer外贸e户通B2B收款简介 | 亚马逊印度站、速卖通和线下B2B收款
【提现】→从派安盈提现到国内 | 外管局关于提款人民币的规定 | 不支持错名提现 | ATM机取款
【消费】→随心付:订购实体卡 | 虚拟卡 | P卡激活和休眠 | P卡到期后更换
Payoneer派安盈咨询微信:ZhaoNiuPai,转载请以链接的形式注明本文地址
本文地址:http://www.zhaoniupai.com/blog/archives/223.html

