昨日,见到封泥“新息国丞”一枚。很高兴!遂试读之。
封泥,又叫“泥封”。我国古代公私简牍大多书写在竹简和木札上,封发时需先用绳子穿连捆缚,然后在绳端或交叉处加以检木,封以泥土,泥上加盖印章作为信验,以防私拆,其泥即称封泥。其在职官与地理方面,填补了较多史料空白①。
这枚“新息国丞”封泥,方寸大小为“通官印”,印文属小篆系统,由所呈封泥文字为朱文印痕可知,原印系阴刻白文。“两汉官印皆出铸造,用白文②。”印文字数有四,上下两排对称布局。内容为复合结构“官署+官名”或“地名+官名”式样③。
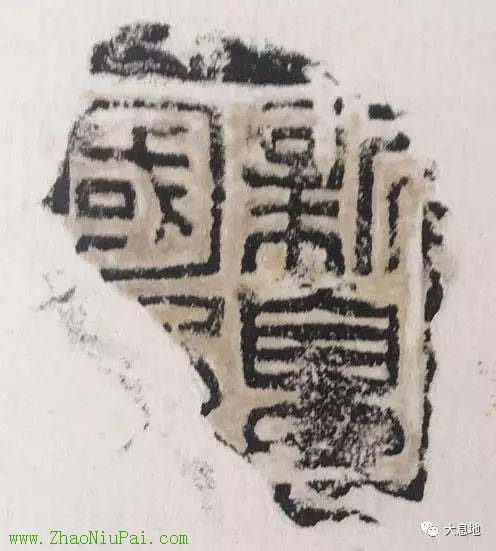
新息国丞泥封
新息,即新息县,今河南省息县。商周时期为息国,由甲骨刻辞可知,早在商王武丁时期,息国就是商朝之重要属国,息族且与商王室通婚,双方关系极为密切。西周初期,始由西周姬姓贵族所代替。《世本•氏姓》篇:“息国,姬姓”,指的就是周代姬姓息国。其地望,文献载于今河南息县境。《左传•隐公十一年》传:“郑、息有违言,息侯伐郑。”杜预注:“息国,汝南新息县。息一本作鄎。”许慎《说文•邑部》:“鄎,姬姓之国,在淮北。从邑,息声,今汝南新息。”《汉书•地理志》载,汝南郡属有县三十七,其第十六为“新息④”。颜师古注引孟康曰:“故息国,其后徙东,故加新云。”是知新息县为西汉初设,隶属汝南郡,且为周代息国故城之所在⑤。
至东汉,则不称新息县,而称“新息侯国”。当然,此“侯国”已不可与姬周分封之侯国同日而语,实为与“县”是同一级行政单位⑥,或其职事略小于“县”。《二十二史考异》云:“汉制,列侯所食邑为侯国。西京侯者封户有多少,所食或尽一县,或止一乡一亭,皆以侯国称之。......恩有降杀,秩无尊卑也⑦。”《后汉书•汝南郡》载曰:“新息,侯国⑧。”
查考而知,东汉时期,新息侯仅两任,一为建武十九年(43)“新息侯马援⑨”,一为建武二十五年(49)“新息侯朱浮⑩”。
该“新息国丞”封泥,必当为此时所用。
马援和朱浮,虽贵为“新息侯”,但却并非新息侯国的治民主官(最高行政长官)。《后汉书•百官志》:“每县邑道大者置令一人,千石;其次置长,四百石,小者置长,三百石。侯国之相,秩次亦如之。”“侯国相,主治民,如令长,不臣也。但纳租于侯,以户数为限”。也就是说,光武帝刘秀为限制这些列侯,不以其为治民主官,而另置侯国“相”(与县长、县令同级)为各侯国治民主官,对列侯不称臣。“每国置相一人,其秩各如本县。本注曰:主治民,如令长,不臣也。但纳租于侯,以户数为限。”这些侯国相要将每年所收的衣食租税,依照皇帝御赐的民户数(列侯所食,或不尽食全侯国户税,仅为其国境户口之一部分)交给列侯享用。实际上是取消了列侯自置官吏、征收赋税的权力。
丞,即县令长侯国相之幕僚属吏佐官。其制始见于战国时代之秦及三晋,秦统一后,诸县仍置丞以佐令。《百官表》云:令长相皆“有丞尉,秩四百石至二百石,是为长吏。”《续百官志》,令长相“丞各一人。”
县丞之职,《通典》记载,除佐令长之外,还“兼主刑狱囚徒⑪”。《续百官志》本注云:“丞署文书,典知仓、狱。”主和典的意思表明,县丞对于令长不完全是辅佐,更不是从属身份,而是能够独立地处理仓狱等事。故,在一县(侯国)之内,丞与令、长一样,也是由中央任命,其地位亦相对较高⑫。
顺便说一下,息县在汉代,当一个“大县”。理由主要有三:
其一,《汉书•百官表》曰:“万户以上为令,秩千石至六百石;减万户为长,秩五百石至三百石。”《续百官志》:“县万户以上为令,不满为长。”“每县邑道大者置令一人,千石;其次置长,四百石,小者置长,三百石。侯国之相,秩次亦如之。”是以县万户以上为令,可谓“大县”。而《汉书•王莽传》载,太后下诏,封大司马新都侯王莽“以召陵、新息二县户二万八千益封⑬”。若此平均而称,则新息县当有一万四千户矣,实属一“大县”耳。
其二,《后汉书•马援传》载,马援平定交趾(今越南)凯旋回朝,朋友都来慰问时,马援“谓之曰:‘今我微劳,猥飨大县,功薄赏厚,何以能长久乎⑭?’”简译一下就是,马援自谦地说:“如今我就这点功劳,却受封一个大县(封为新息侯),功少赏多不能长久啊!男人应战死边疆,马革裹尸,岂能老死于床上?”
其三,《新出汝南郡秦汉封泥集》一书,录有“新息左尉”封泥两枚。既有“左尉”,亦必当有“右尉”(只是暂时未见)。《续百官志》,令长相“尉,大县二人,小县一人。”能有“左右二尉”者,自当为一“大县”。
注释:
①周晓陆《秦封泥所见江苏史料考》。
②罗福颐:《古玺印概论》,第6页。
③吴勇、田小红、穆桂金《楼兰地区新发现汉印考释》2016年2期。
④《汉书•卷二十八上•地理志•第八上》。
⑤李伯谦《后李商代墓葬族属试析》,《中原文物》1981年4期。
⑥严耕望《中国地方行政制度史甲部---秦汉地方行政制度》。
⑦《二十二史考异•九•侯国考》。
⑧《后汉书•志第二十•郡国二•汝南郡》。
⑨《后汉书•卷二十四•马援列传•第十四》。
⑩《后汉书•卷三十三•朱冯虞郑周列传•第二十三》。
⑪《通典》卷三三。
⑫《秦汉官制史稿》。
⑬《汉书•卷九十九上•王莽传•第六十九上》。
⑭《后汉书•卷二十四•马援列传》。
来源:大息地
如需注册Payoneer派安盈,欢迎使用【野猪尖的推荐链接】进行注册,成为我的推荐客户,后续在使用派安盈时遇到问题能获得专属咨询服务,也可协助申请1%或更低的费用优惠。请注意,若打开Payoneer官网来注册,是没有上述优惠的。Payoneer注册咨询,+微信号:ZhaoNiuPai
【野猪尖的推荐链接】 http://ZhaoNiuPai.com/Payoneer.html
复制上述链接到浏览器打开,或扫码注册Payoneer派安盈
【Payoneer派安盈申请教程:个人账户、企业账户、随心付虚拟卡】
======【Payoneer派安盈注册与使用指南,野猪尖整理于2013→2026年】======
【注册】→Payoneer个人账户注册教程 | 公司账户申请教程 | 地址证明和证件 | 注册被拒绝
派安盈个人和公司帐户的区别 | 如何注销P卡 | 买卖P卡的风险 | 更换密码及手机号 | 更换邮箱
【币种】→美元电汇 | 欧元 | 英镑 | 日元 | 加元 | 澳元 | 墨西哥 | 港币和迪拉姆 | 币种转换
【官方】→秉承公正、公开、透明服务 | 封号原因 | 最新政策 | 答疑手册(FAQ) | 手机App
联系客服 | 费用表 | 年费 | 如何减少Payoneer手续费 | 跨境收款服务商拷问
跨境电商论坛:2019年 | 2018年 | 2017年 | 2016年 | 2015年 | 直播回放 | 橄榄枝计划
【收款】→亚马逊绑定派安盈 | 更换收款帐户 | 收款方式对比 | 账户对账单 | 子账户和KYC证明
提前放款服务 | 跨境电商/外贸收款方式对比 | VAT缴费(答疑) | 如何评价Payoneer派安盈
最新平台:Chewy | Chewy入驻 | Trendyol及其它独家平台 | TikTok直播 | TikTok Shop
老平台:PayPal | Wish | 虾皮Shopee | 俄罗斯Joom | 东南亚Lazada | 非洲Jumia
eBay | 拉美Linio | 美客多Mercado Libre | 新蛋Newegg | 沃尔玛Walmart | 苹果开发者
法国乐天 | 法国CDiscount | 德国乐天、Real.de、eMAG、Wayfair、京东印尼 | 波兰Allegro
如何向Payoneer充值 | 如何用Payoneer派安盈收款 | 请求付款(答疑) | 收款审核时“待定”
Payoneer外贸e户通B2B收款简介 | 亚马逊印度站、速卖通和线下B2B收款
【提现】→从派安盈提现到国内 | 外管局关于提款人民币的规定 | 不支持错名提现 | ATM机取款
【消费】→随心付:订购实体卡 | 虚拟卡 | P卡激活和休眠 | P卡到期后更换
Payoneer派安盈咨询微信:ZhaoNiuPai,转载请以链接的形式注明本文地址
本文地址:http://www.zhaoniupai.com/blog/archives/225.html

