查看本文最新版:学宫冒籍,清代的异地高考
最近有两条新闻非常切合本文的主题,一条是仝卓实力坑爹:2020年5月22日,因电视节目《声入人心》出名的歌手仝卓在直播中分享自己当年考学的压力,聊起当年复读时“往届生变应届生”的经历,其继父仝天峰最终被免职。
另一条是山东冠县“农家女被冒名顶替上大学”:2004年10月,20岁的考生陈春秀最终没有等来她的高考录取通知书,决定去几百公里外的烟台市打工;另一边,18岁的考生陈艳平却拿着陈春秀的录取通知书,前往山东理工大学报到,成为一名大学生。
在先贤先儒、祭礼祭品之后,继续连载《连平州志》第四卷“学宫-附籍”。卷四学宫的篇幅较长,这是第3篇,又是5000余字,但还没完,后面还有乡饮酒礼。欢迎关注照牛排的微信公众号(iZhaoNiuPai)——

据说明末刚建州时连平学宫里的学生很少,为避免学校空虚而允许外地人来连平报考,之后东莞、顺德、江西、福建等地生员纷纷涌入,本地文武考生不足200人,而来自外地的冒籍者竟有120多人。最后顾及连平荒僻新建,把冒籍者改回原籍了事。

科场条例严密,亲族须回避,考生不得冒籍,不得夹带,入闱时须点名搜检
所谓冒籍即假冒籍贯,用今天的话说就是“异地高考”、“科考移民”。明清之际,各省参加科举考试的生员名额及录取名额均有限定,士子参加考试必归于本籍(亦可在本籍与寄籍中作一选择)投考,不得越籍赴试。但有的生员投机取巧,假冒他省之籍投考,称为冒籍。比如乾隆年间各地乡试的录取率:文化大省江苏是5.5,落后地区云南是53.8,贵州是21(单位:百万分之一)。落后地区的录取率是发达地区的几倍,这就使得教育发达地区的考生通过过继、投亲、买地、冒名、串通官员等五花八门的手段,到边远低分地区参加高考,影响社会的公平与稳定。唐代大诗人白居易也曾冒籍,这个祖籍山西、出生河南、户籍陕西的大诗人,竟跑到安徽宣城参加“高考”。
为杜绝科举冒籍现象,康熙年间开始对考生进行“审音”。乾隆十年,在顺天乡试时,朝廷特派满、汉御史各一人参与“审音”,被称为“审音御史”,通过考生的口音和祖坟所在地来辨认考生的籍贯。

广东贡院是两广举行乡试、考选举人的场所,与顺天贡院、江南贡院、河南贡院并称“清代四大贡院”
【附籍】
韩志曰,新建之治学校岂容空虚,附籍之设无非欲实庠序,暇计日后法弊相生,遂滋蔓不绝乎。查顺治十六年(1659年)冒籍:张文灼、陈宜登、杨进标,亦借附籍之名冒进州庠,刘守懋德通详革除在案。
于康熙七年(1668年),州守高光国以冒籍纵横等事申详,各宪奉批镌碑,严禁称昔日之附籍即今日之土著。斯附籍之名除之已久,而异棍不得复借冒矣。
康熙十九年,(佟)国瑞来牧斯州,见子衿寥寥,细阅学册而知,又遭异府异邑之人为,或赴藩司,或赴学宪,具呈援例,俱未由州故也。及康熙壬戌(1682年)、丙寅(1686年)两科亲送道试,冒籍锢弊为一痛除矣。
今奉督学黄通行岁考,随奉抚都院朱宪牌,为严禁生童冒籍等事在案,随据州庠文武生员具呈到州看详,去后蒙批督学拨行在案。而冒籍文武生员共120余名,现拨原籍查收入册。而连平膠庠积数十年来之冒滥,至今日乃得清除也。仍载附志,俾后人有所鉴观焉,《院道严禁冒籍》碑文于左——

广东贡院明远楼,广东巡抚李士桢重建于康熙二十三年(1684年),2016年重修
惠州府连平州为严禁生童冒籍,以厘积弊事,康熙二十七年(1688年)八月初七日蒙本府信牌,康熙二十七年七月二十一日奉抚都院朱宪牌,照得士子读书志期上达,若冒籍考试,功令首严查条例内开冒籍之禁令。各直省学臣特严廪生保结之法,诸生童凡有籍贯假籍者,不论已未入学,定行黜革,将廪保懲黜不宥。
至康熙十六年礼部具题,凡现在各省举监生员,如有冒籍者,俱令呈明改回原籍。奉旨允行,俱经严饬在案,今查粤东向来考试多系冒籍顶名,不由府州县考较,但于送道之时钻刺夤缘附名册末,及至道取发案共见诧异,谓本处平日并无是人,该州县官未尝识名,该学教官总未会面。入泮者多系冒籍,土著子弟十无二三,致生童失意灰心,鲜习举业,山僻文风愈加不振,无怪乎各生童纷纷具诉并各属条议及此也。
本都院奉命抚粤务,期振兴文教,积弊当为祛除,合行严饬,备牌行府仰州遵依出示晓谕,严饬仍牒行儒学一体,遵照在案。今于本年十一月初六日,据通州文武生员梁世安等连名具呈,为披陈冒滥积弊恳详改回原籍,以彰功令,以肃学政事。窃闻朝廷较士首严冒滥故,画疆定额,就地取才,毋容诡竄入籍痛。

广东贡院明远楼,摄于1873年,是贡院的最高建筑,用于监考
连平建自明末,始因招徕受㕓,在城准其附考州籍,膠庠土著不满二百。冒籍纳名与奉例捐纳文武生员,有东莞、顺德各县人,有江西、福建各省人,共一百廿余人。不经州试,地隔千里,师长不识,庠友莫认,或张冠李戴,兄故弟顶。遇考则有僱倩之弊,丁尤则有假揑之情,皆因学师远距无由查核。侥幸食廪搀越间次顶补,故缺任其巧餙,宫墙冒滥莫如连平为甚。
兹奉抚院大老爷牌行,为严禁生童冒籍以厘积弊事,蒙示晓谕环读之下,仰见振兴山僻文风至意,正连庠土著单寒下士披云见日时也。伏仰朝廷宽例,凡冒籍生监准令自首改正免革,具报礼部。今连平荒僻山州不及中邑,难堪冒籍之害,只得连名呈恳赐文,详请将冒籍文武生员一百二十余人照例改回各生原籍,庶土著培而宫墙肃矣。

广东贡院的号舍,是考生考试和住宿之所,位于明远楼两侧东西文场内,每排以《千字文》编号
等情并开文武冒籍生员册一本,到职据此随该卑职看得连平州建自明末,原系四县分割。膠庠土著不满二百,而从前竄籍冒滥与奉例捐纳,或纳府名附寄,不经州试者则有一百二十余人。皆距县异府,地界窎远,学师庠友面未识认。凡遇考较不无僱倩代替,冒占前列,侥幸食廪。兼有父亡子顶、兄终弟继,揑假丁尤更难稽察,总缘荒僻小州视为捷径,遂致阻抑土著上进之路。
恭遇宪台抚粤,兴除利弊,严禁冒滥,奉檄晓谕,山陬遐壤,欢呼动地。兹据通州生员梁世安等联名具呈造册,前来相应,具文详请宪台垂恩勅行酌夺,将冒籍文武生员朱贵等查照原籍改回本学。听各该学稽察粮务,严杜丁尤僱倩作姦等弊,俾荒州士子咸自振兴,争自濯磨,获邀上进以丕文教,叩诵作育,宏慈奕祀,靡有已也。

乡试九天六夜,照牛排 www.ZhaoNiuPai.com
等缘由蒙提学道黄批仰候查详,抚宪饬行缴。兹奉巡抚批仰,提学道确查详夺,缴册并发奉此拟合就行备牌,仰府照依宪批详内事理。即将连平州所详后开生员朱贵等冒籍情由逐一确查明白,具详本道复核以憑转详抚都院批夺。等因蒙此案照先,据该州详同前事,连缴冒籍生员姓名册一本到府,据此当批仰候抚都院学道批示缴册存查,业经印发在案。
今蒙前因,除将学道牌开并该州详缴前册内,开广、惠二府所属文武各生,查照原籍列名行县,确查都图籍贯,并某年月日冒进州庠注明册内,缴府详缴学道,转详抚都院批夺在案。

在广东贡院旧址发掘的考生遗物:碗、茶壶、油灯,还有便盆
《牟志》曰,稽古建国立都多旌四方文学之士以实京雍肆,是开疆设郡咸立新籍,凡以广招徕育楩梓也。先奉南赣抚院潘发册八欵,下问内一欵,该州既设有学宫师长,有无诸生肄业,或择他郡文章尔雅、行谊端醇者为之启蔽发蒙,其民间子弟稍通文墨应否行,学道破格作养以永鼓舞。因遵详请议设附籍严立禁约,既详且悉。荷蒙督学道魏(浣初)垂念岩疆,加意作人、量取新生不礙土著之额,一时负笈之士闻风继至,然而土民之未广者率相聚攻讦,殊失创始作新之至意。俟学校渐次充实,附籍亦为土著,将不禁而自息矣。
详文——
惠州府连平州为边城,初建增广诸生以实庠序,以成州制事。窃照岩险重城,方招庶民以充实荒天昧色,尤资庶士以作新州制创立。万山割附四里,迄今城内茅房数十间,二三士民落落晨星。先是未奉题准,维时送考童生仅八十余名,蒙前学道曾考取二十四名,暂寄和、河四县。案末候州官到日送学作养,已开薪槱之门,用闢彚征之路。
近蒙提学行文彚考,生童远近闻风争思负笈,值四图诸童指称冒籍,互相攻讦,一时真赝几于莫辨。本州俯顺民情,四图之外概不准考,已经开册听候考夺。伏思建学之始正異扩充如止,据四图有限人民尽居村落,城内学校何时充实合无。比照各省改土设学事例,凡属土著为土民籍,其辐辏归顺,受厘立业,纳粮输差者为客民籍。送考之日另开一册,或广收土著,既足以服其心,即量取客民,亦非以侵其数。惟未经立籍、未纳粮饷者即系冒籍,定不姑容,以滋倖冒庶弊清蠧涤,渐觉杞梓之育成,近悦远来,行看菁莪之蔚起,边城黉序禆益非浅鲜矣。

《连平州志》卷之四:学宫附籍
事关学政,匪卑职所敢专擅也,为此将今缘由理合具申,伏候照详施行。奉提学道魏(浣初)批,该州百事创始,既有民社之司,合广庠序之教,准照罗定州事例,分编土著、附籍两项如详覈确。其未经立籍纳税者毋得滥收滋弊,缴学道魏(浣初)告示,示谕连平州生童知悉。尔州土著、附籍区分二册,盖皆本道仰体虔抚作新至意,而州官又曲体本道作人一念,照罗定州已行之法剏立规模,无非招徕以实版图,遂鼓舞英髦以奠学校也。
尔等果皆家絃户诵,人善操觚,亦何必借才错壤,多此一事?今本道秉十分恕道,鑑尔等三分文气,取数视他邑之小者已不为不多矣,何尚纷纷告扰。姑念志在进取,再加覆阅拔取十名于土著之内,不惟他邑,不得引取以希滥恩,即尔州后日不得据此以成定额。如再烦言抗挠,本道则有三尺,毋致求荣反辱进寸退尺,自贻伊悔特示。
魏(讳浣初,常熟人,丙辰[万历四十四年,1616年]进士,曾任广东提学参政)。
注释:滋蔓【滋长蔓延】,藩司【明朝时承宣布政使司的辖区是国家一级行政区,简称“布政使司”、“布政司”、“藩司”、“行省”。布政使司设左、右承宣布政使各一人,即一级行政区最高行政长官。而一省之刑名、军事则分别由提刑按察使司与都指挥使司管辖。布政司、按察司、都司合称为“三司”(从二品),皆为省级行政区最高机关。清朝时在各省布政使之上设置固定制的总督、巡抚,掌管全省军民事务。布政使成为巡抚属官,专管一省或数个府的民政、财政、田土、户籍、钱粮、官员考核、沟通督抚与各府县】,
学宪【即学政,全称“提督学政”,亦称“督学使者”、“学台”。学政是明清派往各省督导教育行政及主持考试的专职官员,每省 1 人】,道试【清代省下设道,道所举行的考试】,膠庠【胶庠,周代学校名。周时胶为大学,庠为小学】,功令【古时国家对学者考核和录用的法规】,懲【同“惩”】,宥【yòu,饶恕】,钻刺【钻营】,夤缘【yín yuán,攀附拉拢关系】,竄【cuàn,同“窜”】,㕓【chán,同“廛”,古代城市平民的房地】,僱倩【出钱雇请】,丁尤【朝廷官员在位期间,如若父母去世,则无论此人任何官何职,从得知丧事的那一天起,必须辞官回到祖籍,为父母守制二十七个月】,揑【niē,同“捏”】,搀越【chān yuè,越出本分,如越职、越权】,餙【shì,同“饰”】,窎【diào,远】,宪台【汉称御史所居官署为宪台,后亦用为地方官吏对知府以上长官的尊称】。

晚清《点石斋画报》上的《南闱放榜图》,展示光绪十七年(1891年)江南乡试放榜盛况
憑【píng,同“凭”】,转详【将案情呈报上级官府】,楩梓【pián zǐ,栋梁之材】,欵【kuǎn,同“款”】,荷蒙【承蒙】,礙【ài,同“碍”】,维时【当时】,负笈【指背着书箱,游学外地】,薪槱【xīn yǒu,亦作“薪楢”,比喻贤良的人才或选拔贤良的人材】,闢【pì,同“辟”】,彚【huì,同“汇”】,辐辏【fú còu,也作辐凑,形容人或物聚集,像车辐集中于车毂一样】,杞梓【qǐ zǐ,原指两种木材名字,后比喻优秀的人才】,菁莪【jīng é,育材】,近悦远来【邻近的人因得到好处而高兴,远方的人也都闻风前来归附】,覈【hé,同“核”】,仰体【体察上情】,曲体【深入体察】,剏【】,【chuàng,同“创”】,英髦【yīng máo,俊秀杰出的人】,家弦户诵【家家都不断歌诵,形容有功德的人,人人怀念,也形容诗文流传很广】,操觚【cāo gū,执简,写作】,鉴【jiàn,同“鉴”】。
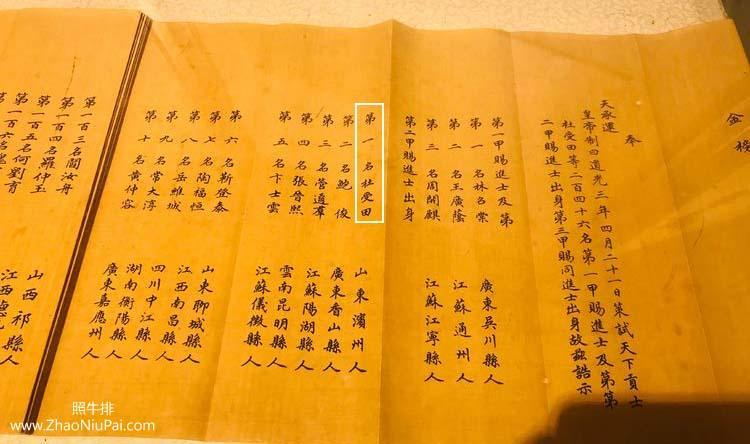
道光三年(1823)金榜,杜受田殿试二甲第一,14年后成为咸丰的老师
参考资料:新华字典,百度百科;
《连平州志》,牟应受、韩师愈、卢廷俊、何深、颜希圣,明清
往期回顾(戳下方标题):
如需注册Payoneer派安盈,欢迎使用【野猪尖的推荐链接】进行注册,成为我的推荐客户,后续在使用派安盈时遇到问题能获得专属咨询服务,也可协助申请1%或更低的费用优惠。请注意,若打开Payoneer官网来注册,是没有上述优惠的。Payoneer注册咨询,+微信号:ZhaoNiuPai
【野猪尖的推荐链接】 http://ZhaoNiuPai.com/Payoneer.html
复制上述链接到浏览器打开,或扫码注册Payoneer派安盈
【Payoneer派安盈申请教程:个人账户、企业账户、随心付虚拟卡】
======【Payoneer派安盈注册与使用指南,野猪尖整理于2013→2026年】======
【注册】→Payoneer个人账户注册教程 | 公司账户申请教程 | 地址证明和证件 | 注册被拒绝
派安盈个人和公司帐户的区别 | 如何注销P卡 | 买卖P卡的风险 | 更换密码及手机号 | 更换邮箱
【币种】→美元电汇 | 欧元 | 英镑 | 日元 | 加元 | 澳元 | 墨西哥 | 港币和迪拉姆 | 币种转换
【官方】→秉承公正、公开、透明服务 | 封号原因 | 最新政策 | 答疑手册(FAQ) | 手机App
联系客服 | 费用表 | 年费 | 如何减少Payoneer手续费 | 跨境收款服务商拷问
跨境电商论坛:2019年 | 2018年 | 2017年 | 2016年 | 2015年 | 直播回放 | 橄榄枝计划
【收款】→亚马逊绑定派安盈 | 更换收款帐户 | 收款方式对比 | 账户对账单 | 子账户和KYC证明
提前放款服务 | 跨境电商/外贸收款方式对比 | VAT缴费(答疑) | 如何评价Payoneer派安盈
最新平台:Chewy | Chewy入驻 | Trendyol及其它独家平台 | TikTok直播 | TikTok Shop
老平台:PayPal | Wish | 虾皮Shopee | 俄罗斯Joom | 东南亚Lazada | 非洲Jumia
eBay | 拉美Linio | 美客多Mercado Libre | 新蛋Newegg | 沃尔玛Walmart | 苹果开发者
法国乐天 | 法国CDiscount | 德国乐天、Real.de、eMAG、Wayfair、京东印尼 | 波兰Allegro
如何向Payoneer充值 | 如何用Payoneer派安盈收款 | 请求付款(答疑) | 收款审核时“待定”
Payoneer外贸e户通B2B收款简介 | 亚马逊印度站、速卖通和线下B2B收款
【提现】→从派安盈提现到国内 | 外管局关于提款人民币的规定 | 不支持错名提现 | ATM机取款
【消费】→随心付:订购实体卡 | 虚拟卡 | P卡激活和休眠 | P卡到期后更换
Payoneer派安盈咨询微信:ZhaoNiuPai,转载请以链接的形式注明本文地址
本文地址:http://www.zhaoniupai.com/blog/archives/221.html


