查看本文最新版:连平学宫(孔庙)的祭礼、祭品和学租
孔子于鲁哀公十六年(公元前479年)去世,翌年,哀公于孔子旧宅立庙守茔,是为孔子立庙之始,亦为山东曲阜阙里孔庙的由来。由于孔子创立的儒家思想对于维护文化和统治所起到的重要作用,孔庙被历代帝王所器重。汉高祖刘邦亲临曲阜孔庙以太牢祭孔,汉武帝“罢黜百家,独尊儒术”,北魏孝文帝下诏令全国各县学祭祀孔子并成为后世的国家礼制,祭孔大典延续了两千余年直到民国,沉寂半个世纪后于1986年恢复。

曲阜孔庙大成殿,属于明清建筑,和故宫很像
清代时中国各地建有2000多座孔子庙,目前保存较完整的孔庙仅60余座。孔庙的主要建筑物包括大成殿、崇圣祠、东西庑、明伦堂、棂星门、泮池等。封建科举制度下,孔庙与学宫相结合,是仕途的起点。《连平州志》第四卷交待完连平学宫(孔庙)里奉祀的先贤先儒,接着讲祭礼、祭品、学租和庠序,连平本地的学宫和祭器已无迹可寻,不过全国的文庙都是一个模子刻出来的,本文配图多取自孔子老家山东曲阜的孔庙。欢迎关注照牛排的微信公众号(iZhaoNiuPai)——

【祭礼】康熙二十年(1681年)颁行学宫祭礼
至圣先师孔子正位:礼神白色帛一,降真炷香一炷,降真香八两,三足白磁爵三,牛、羊、豕各一,登一,铏二,簠、簋各二,笾十(白饼、黑饼、形盐、蒿鱼、鹿脯、枣、栗、榛、菱、芡),豆十(脾析、豚胉、鹿醢、兔醢、鱼醢、醯醢、韭、菁、笋、芹),酒一罇(照牛排注:孔子的祭品等级可谓顶配,品种最全,而四配十哲及东西两庑先贤先儒的祭品都是逐级删减,甚至共用)。
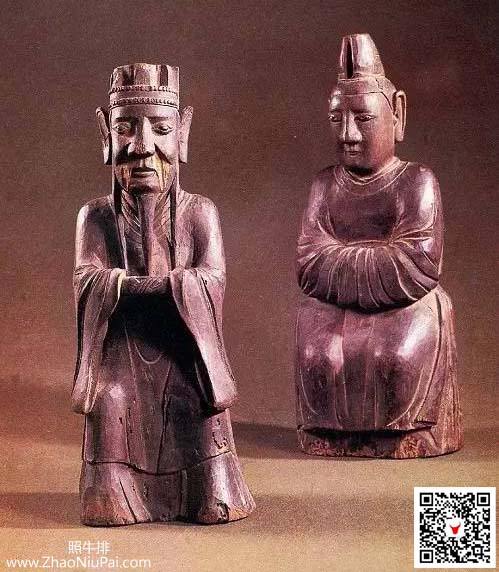
孔子夫妇楷木像,传为子贡手刻,曾流落浙江衢州,现藏于山东曲阜孔庙

祭孔礼器:登,这个是孔子专享的
四配:每位一案,帛一,降真炷香一炷,降真香四两,三足白磁爵三,羊、豕各一,铏二,簠、簋各二,笾、豆各八。
东西旁配位各五位:每位一案,每案降真炷香一炷,降真香四两,三足白磁爵各一,豕肉一块,铏一,簠、簋各一,笾、豆各四。五位共帛一,共磁爵三,豕首一。

祭孔礼器:铏
东庑四十九位:每二位一案,计二十五案。每案铜爵三,豕肉二块,簠、簋各一,笾、豆各四。共帛一,降真炷香一炷,降真香八两,共铜爵三,豕首一。
西庑四十八位:二位一案,设同东庑。

祭孔礼器:清雍正兽面纹铜簠
乐奏六佾,文生三十六人。
乐器:钟十六口,磬十六面,琴六张,瑟四张,箫笛六枝,排箫二架,埙一箇,笙六攒,大皷一面,搏附皷二座,柷一座,敔一座,木笏六面,羽籥二十六副,麾旙一首,旌节二首。
每项用乐舞生一名,每人着红色补服,系绿绸带,戴铜顶裹金凉帽或暖帽。

曲阜国际孔子文化节祭孔乐舞,六佾or八佾
迎神乐奏《咸平》之曲,行三跪九叩首礼。
初献乐奏《宁平》之曲,正官至位前行一跪一叩礼。立献帛、爵毕,行一跪一叩礼。立读祝官至安祝文,桌前行一跪三叩礼。将祝文捧立在桌左边,正官复读祝位立,乐止。
正官、各官、乐舞生俱跪读祝,官读祝毕,至正位奠帛,桌前盛帛盒内跪安,行三叩礼,乐舞生起立奏乐,各官行三叩礼立。正官就四配位前各行一跪一叩礼,立献毕各行一跪一叩礼,分献官照正官行礼,分献毕,正官、分献官复位立。

曲阜孔庙祭孔大典,2019年9月28日是孔子诞辰2570周年纪念日
亚献乐奏《安平》之曲,正官、分献官照初献礼,献毕复位。
终献乐奏《景平》之曲,照亚献礼,献毕复位。乐毕,文生执旌节引退于两旁立。
赐福胙,正官诣受福胙位,跪受胙,饮福酒毕,行三叩礼复位,行三跪九叩礼。
彻馔乐奏《咸平》之曲,送神乐奏《咸平》之曲,行三跪九叩礼,乐毕诣望燎位,焚祝帛,礼毕。

祭孔礼器:簋
祭启圣王,行三跪九叩礼,仪同前。供品:礼神白色帛一,降真炷香一炷,降真香四两,白磁爵三,羊、豕各一,铏二,簠、簋各二,笾、豆各八,酒一罇。
东西配先贤四位。
东西庑先儒四位:每位一案,每案降真炷香一炷,降真香四两,铜爵三,豕肉一块,簠、簋各一,笾、豆各四。二案共礼神白色帛一,豕首一。
雍正二年(1724年)颁行祭品,奉㫖用大牢自秋祭始
先师(孔子)正位陈设:礼神制帛一(白色),白磁爵三,牛一,羊一,豕一,登一,铏二,簠二,簋二,笾十,豆十,酒罇一。

曲阜孔庙大成殿内的孔子像,清雍正黄地彩绘缠枝牡丹纹铜胎画珐琅五供
四配位陈设:每位礼神制帛一(白色),白磁爵三,羊一,豕一,铏一,簠二,簋二,笾八,豆八,酒罇一。
十哲陈设——东五位(五案),又朱子一位一案:礼神制帛一(白色),白磁爵各一,豕一,铏各一,簠各一,簋各一,笾各四,豆各四,豕首一。
西五位(五案,与东五位陈设同)。

祭孔礼器:笾
东庑陈设:礼神制帛一(白色),铜爵各一,豕三,每案簠一,簋一,笾四,豆四。
西庑陈设(与东庑同)。
崇圣祠正位陈设(五案):每位礼神制帛一(白色),白磁罇三,羊一,豕一,铏一,簠二,簋二,笾八,豆八,酒鐏一。

祭孔礼器:清乾隆铜豆
配位陈设(每位一案):礼神制帛二(白色),豕首一,每位铜爵三,簠一,簋一,笾四,豆四,豕肉一。
东西两庑陈设:礼神制帛二,每位铜爵三,簠一,簋一,笾四,豆四,豕肉一。
名宦、乡贤二祠同时分祭,仪同两庑。照牛排(www.ZhaoNiuPai.com)。

祭孔礼器:爵
【学租】(附载)
学前左侧店地七间,右侧店地三间(俱收租归儒学)。
学内一切旷地俱属儒学。
忠信图三角等处田种。
浰头土名,田种。
【庠序】(前志以学宫列建置内,因附籍事复分庠序一门,今合之附学宫后)
牟志曰,国家自辟雍以至郡邑皆有庠序,所以兴贤育才、维持世教,关系匪浅鲜也。州庠肇始,诸弟子员或分割或新进,彬彬若而人徙此,鸿飞鹏举扶摇而上九万里,拭目竢之,吾愿诸弟子为贤士不为凡民也。
和平县分拨廪生陈易简等十名,河源县分拨廪生黄可遇等五名,长宁县分拨廪生赖上昇等一十九名,翁源县分拨廪生谢挺等一十三名。
益以两案新进吴进、叶自育、吴子昌等共一百余名,不及东粤一下县。尚赖督学道广开薪槱,溢格滋培庶于创始,黉宫大有造云。

唐代吴道子《先师孔子行教像》,清代石刻,现存于曲阜孔庙。德侔天地,道冠古今,删述六经,垂宪万世
注释:降真香【其香似苏枋木,烧之烟直上,能入药。亦名鸡骨香、紫藤香。降真香是古代帝王贵族、文人及道家最喜欢用的一种香,平民百姓大多是用不起降真香的。《本草纲目·木部·降真香》云:“拌和诸香,烧烟直上,感引鹤降。醮星辰,烧此香为第一,度功力极验。降真之名以此。”传说能降神,也就是引来仙鹤飞舞盘桓,是能够沟通天界、延请神灵降临醮坛的灵香】,豕【shǐ,猪】,登【祭孔礼器,又称“镫”,形如今之高足盘。是古代盛放熟食的器具,也指祭祀盛肉食的礼器。《尔雅·释器》:“瓦豆谓之登”】,铏【xíng,古代盛羹的小鼎,两耳三足】,簠【fǔ,古代祭祀时盛稻粱的器具】,簋【guǐ,古代盛食物器具,圆口,双耳】,笾【biān,古代祭祀和宴会时盛果品等的竹器】,形盐【特制成虎形的盐】,罇【zūn,古同“罇”“樽”,古代的酒杯】。
佾【yì,古代乐舞的行列,六佾是指六行六列共36人,是周制诸侯的等级】,埙【xūn,古代用陶土烧制的一种吹奏乐器,圆形或椭圆形,有六孔。亦称“陶埙”】,皷【同“鼓”】,柷【zhù,古代打击乐器,像方匣子,用木头做成,奏乐开始时敲打】,敔【yǔ,古代打击乐器,奏乐将终时,击之使演奏停止】,笏【hù,古代大臣上朝拿着的手板,用玉、象牙或竹片制成】,籥【yuè,同“龠”,古代乐器,形状像】,旙【fān,同“幡”,用竹竿等挑起来直着挂的长条形旗子】,旌节【古代使者所持的节,以为凭信,后借以泛指信符】。
《咸平》之曲【清顺治十三年,第一次颁定国学释奠乐章,作为释奠孔子之用,采用全新乐章诗词,乐章名将明朝所用乐章中的“和”字改为“平”。新订六乐章为迎神用“咸平”、初献用“宁平”、亚献用“安平”、终献用“景平”、彻馔用、送神用“咸平”,仍沿明制采“六章六奏”方式,舞用六佾、三献均用文德之舞】,胙【zuò,古代祭祀时供的肉。】,望燎【望祭与燎祭,按大祭礼制规定,每次大祭要焚烧纸一万张、金银箔一万锭。烧祭时主家人要站在月台西南角的“望燎位”上观看,以尽孝道。这种仪式叫“望燎”,是祭祀最后一道程序】。
启圣王【孔子的父亲叔梁纥(公元前622—公元前549年),子姓,孔氏,名纥,字叔梁,宋国栗邑(今河南商丘夏邑县)人,是周代诸侯国宋国君主的后代,为逃避宋国战乱,流亡到鲁国昌平陬邑(今山东曲阜)。他人品出众,博学多才,能文善武,曾官陬邑大夫,年近七十生孔子】。
大牢【“牢”是关牲畜的栏圈,古时人们把祭祀时用的牲畜叫做“牢”。祭祀时并用牛、羊、豖三牲的叫做“大牢”,也称“太牢”。太牢用于隆重的祭祀,按古礼规定,一般只有天子、诸侯才能用大牢,孔子用的也是大牢】,庠序【xiáng xù,西周时指地方办的乡学,旧时用来泛指学校或教育事业】,竢【sì,等待】,薪槱【xīn yǒu,亦作“薪楢”,比喻贤良的人才或选拔贤良的人材。《诗·大雅·棫朴》:“芃芃棫朴,薪之槱之。”毛传:“槱,积也。山木茂盛,万民得而薪之;贤人众多,国家得用蕃兴”】,黉【hóng,古代称学校】。

占地327亩的山东曲阜孔庙建筑群
参考资料:新华字典,百度百科;
《连平州志》,牟应受、韩师愈、卢廷俊、何深、颜希圣,明清;
往期回顾(戳下方标题):
如需注册Payoneer派安盈,欢迎使用【野猪尖的推荐链接】进行注册,成为我的推荐客户,后续在使用派安盈时遇到问题能获得专属咨询服务,也可协助申请1%或更低的费用优惠。请注意,若打开Payoneer官网来注册,是没有上述优惠的。Payoneer注册咨询,+微信号:ZhaoNiuPai
【野猪尖的推荐链接】 http://ZhaoNiuPai.com/Payoneer.html
复制上述链接到浏览器打开,或扫码注册Payoneer派安盈
【Payoneer派安盈申请教程:个人账户、企业账户、随心付虚拟卡】
======【Payoneer派安盈注册与使用指南,野猪尖整理于2013→2026年】======
【注册】→Payoneer个人账户注册教程 | 公司账户申请教程 | 地址证明和证件 | 注册被拒绝
派安盈个人和公司帐户的区别 | 如何注销P卡 | 买卖P卡的风险 | 更换密码及手机号 | 更换邮箱
【币种】→美元电汇 | 欧元 | 英镑 | 日元 | 加元 | 澳元 | 墨西哥 | 港币和迪拉姆 | 币种转换
【官方】→秉承公正、公开、透明服务 | 封号原因 | 最新政策 | 答疑手册(FAQ) | 手机App
联系客服 | 费用表 | 年费 | 如何减少Payoneer手续费 | 跨境收款服务商拷问
跨境电商论坛:2019年 | 2018年 | 2017年 | 2016年 | 2015年 | 直播回放 | 橄榄枝计划
【收款】→亚马逊绑定派安盈 | 更换收款帐户 | 收款方式对比 | 账户对账单 | 子账户和KYC证明
提前放款服务 | 跨境电商/外贸收款方式对比 | VAT缴费(答疑) | 如何评价Payoneer派安盈
最新平台:Chewy | Chewy入驻 | Trendyol及其它独家平台 | TikTok直播 | TikTok Shop
老平台:PayPal | Wish | 虾皮Shopee | 俄罗斯Joom | 东南亚Lazada | 非洲Jumia
eBay | 拉美Linio | 美客多Mercado Libre | 新蛋Newegg | 沃尔玛Walmart | 苹果开发者
法国乐天 | 法国CDiscount | 德国乐天、Real.de、eMAG、Wayfair、京东印尼 | 波兰Allegro
如何向Payoneer充值 | 如何用Payoneer派安盈收款 | 请求付款(答疑) | 收款审核时“待定”
Payoneer外贸e户通B2B收款简介 | 亚马逊印度站、速卖通和线下B2B收款
【提现】→从派安盈提现到国内 | 外管局关于提款人民币的规定 | 不支持错名提现 | ATM机取款
【消费】→随心付:订购实体卡 | 虚拟卡 | P卡激活和休眠 | P卡到期后更换
Payoneer派安盈咨询微信:ZhaoNiuPai,转载请以链接的形式注明本文地址
本文地址:http://www.zhaoniupai.com/blog/archives/220.html